In this article I will go through my findings and analysis on the Safe Links feature of Microsoft’s Office 365 Exchange Online Advanced Threat Protection.
Tag: office 365
Office 365 Quarantine Tool
If you find yourself using the Office 365 (Exchange Online) e-mail quarantine often then you probably know how frustrating and slow it can be to quickly find and release quarantined items. Often times you’ll find yourself waiting for a few minutes only to realise it’s not doing anything. Then you have to refresh the page and re-enter your search criteria. The fact you can’t even wildcard searches is also unforgivable (it’s 2016 Microsoft, why can we not wildcard search the subject and sender fields?!)
This annoyance coupled with my eagerness to play with PowerShell led me to develop a quick and dirty quarantine tool or viewer if you like. The tool is quite basic but it will let you do the following:
- Wildcard search the subject and sender fields
- Configure the number of results to return
- Release a message based on message ID
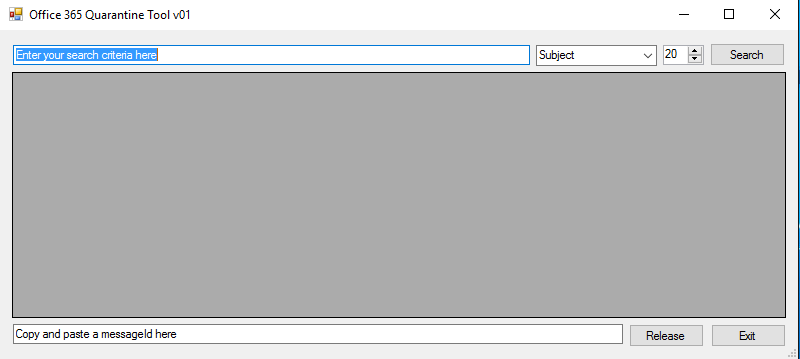
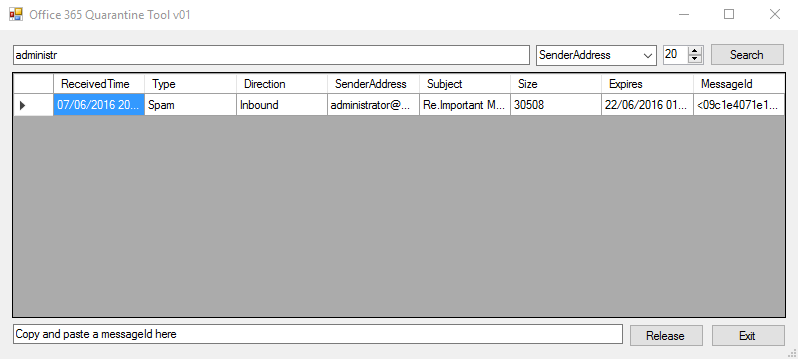
If you want to have a play with the tool, it’s on my GitHub along with the source code if you feel like suggesting some improvements.
In this article I will show you how to create Exchange Online mailboxes in a hybrid environment such that the maiboxes also show up on the on-premises Exchange server management console.
The most logical way of creating an Exchange Online mailbox (you’d think) is to let AD users DirSync across to 365, assign them licenses and be done with it. However doing it this way doesn’t create a link between Exchange Online and your On-Premises Exchange server which means you can’t do things like manage the user’s mailbox from EMC or migrate the mailbox between on-premises and Exchange Online.
Licensing Office 365 users manually can be a tedious task; especially if you are tasked with licensing hundreds or even thousands (think educational institutes that need to license user’s every semester or academic year).
I created a fairly basic script that will take a .CSV input and license your users according to your Office 365 environment and the licenses you have available.
The short answer is, yes.
The long answer is that it will require a lot of work on your behalf.
The new Office 365 midsize business plan is very similar to the E3 plan (bar some advanced features which most users probably won’t need anyway) without the more expensive price tag attached to it; for UK users this is £9.80 per user per month as compared to £15 per user per month… if you have a lot of users the cost adds up very quickly.