In this quick how-to I will show you how you can very easily and quickly run a packet capture on a Palo Alto management interface.
Some reasons why you may want to capture packets on the management interface is to capture traffic such as RADIUS and Syslog which is processed via the management plane. Management traffic cannot be captured using the ‘packet capture’ feature on the GUI so we need to do it using the CLI.
- First SSH to the Palo
- Now we use the tcpdump command to start capturing. It is optional to create filters but I would recommend doing so if you are looking for specific trafficIf you want to capture packets from a specific IP address then you would use something like this:
tcpdump filter "src 10.70.0.1"
to a specific address:
tcpdump filter "src 10.70.0.1"
to or from a specific address (both sides of the conversation)
tcpdump filter "host 10.70.0.1"
specific port
tcpdump filter "port 514"
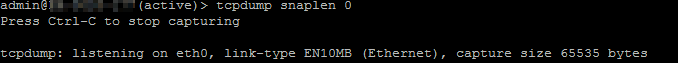
Note that by default only 68 or 96 bytes of data will be captured per packet depending on which hardware model you have. You can use the option snaplen to determine how many bytes you want to capture. Enter snaplen 0 to capture the entire packet. For example:
tcpdump filter "host 10.70.0.1" snaplen 0
You’ll see something like this:
- When you are happy that you have captured enough traffic, simply press CTRL+C to stop.
Now it’s time to export the capture so we can view it in Wireshark. The Palo supports exporting via SCP or TFTP. I chose to use the latter as it literally takes less than a minute to set up a TFTP server on a Windows machine.
Download the mini-portable TFTP server here. Make sure you select the ‘zip’ version if you want the portable version (i.e., no installation).
When you run the tool, it requires no configuration although you may need to allow port 69 on your local machine’s firewall (I did). - Now run the tftp export command on the Palo. It should only take a few seconds to get the capture off the Palo and on to your machine. Replace 10.10.10.10 with your machine’s IP.
tftp export mgmt-pcap from mgmt.pcap to 10.10.10.10
All done! That’s how you run a packet capture on a Palo Alto management interface using TCPDump.
If you by chance already have a SCP server set up then the command will start with scp and follow a similar format.