I’ve cheekily phrased this blog article as a best practice guide to setting up/configuring your Cisco IronPort email security appliance. However I must make clear that the below is what I deem to be best practices/configuration. Every environment is unique so please make sure you understand what you are doing before attempting to implement any of my suggestions below. So, let’s get started! The suggestions below are in no particular order.
Quarantines
- It is a good idea to create separate quarantines for different items you expect to be in the quarantine. For example, it is easier to manage your quarantines if there is a one for ‘bad’ attachments, one for URL filtering, etc.
Incoming Content Filters
- Have a content filter to block actively exploited threats. For example, I have a content filter called quarantine_active_exploits that blocks .rtf attachments (because of the recent Microsoft RTF 0-day that can execute code just by viewing an attachment in Outlook) and bounces back a message to the sender to inform them that their message has not been delivered, the reasons why and what they can do to get their message to go through. Obviously once the exploit is patched, the content filter will be modified to reflect that.
- A content filter to block executables or allow ONLY certain extensions is definitely a must for an email security appliance. Either have a content filter to block a list of ‘dangerous’ extensions (don’t bounce any of these messages) or one that will only allow a list of ‘safe’ extensions. The latter is obviously more secure but will probably cause you more of a management overhead/annoyance in the long run 😉
- A content filter to quarantine failed SPF messages will help reduce the number of spam/phishing messages coming through your environment. SPF is basically a DNS record which states which hosts are allowed to send on behalf of a domain. So for example, only 100.100.100.100 is allowed to send from example.org. If your IronPort sees a message from example.org with the IP 200.200.200.200, it will be quarantined as the owners of example.org have said that nothing other than 100.100.100.100 is to be classed as legitimate. SPF is slowly becoming more and more popular; I recommend you set up SPF for your domain too if you can.
- Add a content filter for URL filtering. Choose your categories as appropriate to your environment but the obvious ones are pornography, illegal downloads, proxy avoidance, etc
Outgoing Content Filters
- A lot of people filter attachment types inbound but forget to do the same for outbound messages. If an internal machine is compromised and starts sending out malware to your customers, you’d probably want IT to be notified so they can identify and fix the issue asap.
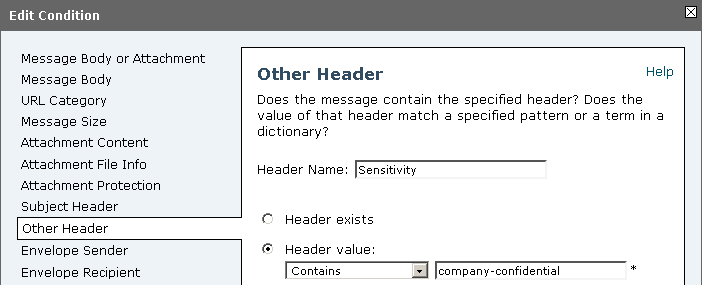
- Encrypt e-mails. Create a policy to encrypt e-mails that contain the word confidential in the subject line or messages with the header sensitivity=company-confidential (this header is set in Outlook when you mark a message as confidential in message composition options)
- I’ll go in to this in more detail later on (in the encryption section) but it is a good idea to create content filters that encrypt messages that contain certain keywords in the message body or even in attachments.
E-mail Encryption
- Edit your encryption profile so that the encryption algorithm is AES-256
- Customise the encryption HTML template and make it a bit more personalised – company logo, policies, who to send an e-mail to if the recipient has troubles opening the encrypted attachment, etc
- Personally I would recommend unchecking the box for Use Decryption Applet. The user experience is a lot better when the recipient doesn’t need to install Java or accept security warnings or other annoying pop-up messages just to open the secure message. I notice no performance or lack of functionality when I disable this checkbox – the secure attachment still opens in the browser – without the hassle
- Select the radio box for Use the Cisco Registered Envelope Service URL with HTTPs.
- This one is very important and I suggest you take some time doing this properly. Talk to all departments in your company and make a list of attachments or e-mail types that contain sensitive information that you/your company does not want to send out un-encrypted. Ideally you will have some example sensitive attachments so you can create unique regular expressions in content filters to encrypt messages that match the sensitive keywords. For example, let’s assume the finance team send out an attachment every month to an outsourced company with all employee salary and bonus details. I would ask the finance team for a copy of this attachment with all the actual numbers and figures blanked out. I would then look for keywords in the document or document name that would not normally be used in other documents. So let’s say this particular attachment has the keyword employee salary details in it. I would then create a regex in a content filter to match this particular keyword and encrypt all messages containing that keyword. Your mileage and environment may vary but it is usually a good idea to do something like this
Host Access Table (HAT)
- Unless you absolutely have to and have no other choice, never put anything in the whitelist/trusted policies; especially if it’s a large subnet of IPs or domains as this could leave you wide open to attacks. If you do need to whitelist some IPs or domains, do NOT disable spam/virus checking otherwise you’re just asking for trouble.
- Edit the default mail flow policy so that:
Max. Concurrent Connections From a Single IP is not more than 2. Your environment may, for whatever reason, require external users more than that but it has never been an issue for me. Normal, well behaved e-mail clients should not open more than 1.
Enable Directory Harvest Attack Prevention and set it to something low. I have mine set to 5. This will stop automated bots from attempting to guess and store a list of valid e-mail addresses
Set TLS under Encryption and Authentication to preferred.
Enable SPF/SIDF Verification
Enable DMARC Verification
Enable Envelope Sender DNS Verification – this hasn’t caused issues for me and it shouldn’t for you assuming sender domains and DNS are properly configured but that can be a dangerous assumption to make - Edit your sender group settings to enable the following: Connecting host PTR record does not exist in DNS. Connecting host reverse DNS lookup (PTR) does not match the forward DNS lookup (A)
- I haven’t done this yet but I do think it is something I will implement soon – adding DNS lists; also known as DNS blacklists (DNSBL) and Real-time blackhole list (RBL). In your sender group settings, there is a field for DNS lists. Add well known, popular sources such as Spamhaus and SpamCop. These blacklists along with the Cisco senderbase network will make your ESA an almost unstoppable force against the evil of spam/malicious e-mail.
Destination Controls
- Change TLS Support to preferred
I hope this has been useful to you! If I have missed anything obvious from the list above, or if you have any comments, please share them below. I plan on creating a part 2 to cover some things I have missed such as DLP, bounce profiles, LDAP queries, and more so stay tuned!
Edit December 2014: Part two has been released!
8 replies on “Cisco IronPort E-mail Security Appliance Best Practices : Part 1”
Nice one.More ironport ftw!
And where is the promised continuation?
It’s coming soon, promise!
Whitelisting doesn’t work with Ironport because of filter behavior with multiple attachements:
http://www.cisco.com/c/en/us/support/docs/security/email-security-appliance/117821-problemsolution-esa-00.html
Thanks for your explanations.
In our environment we operate a blacklist approach so never came across this issue but interesting nonetheless.
I would have thought the IronPort would drop the message or remove the attachment at the very least.
Might do some testing with this to confirm the behaviour in the latest version of AsyncOS.
Are there any repercussions for changing TLS from Off to Preferred?
Hello Khaim,
As far as my knowledge and experience on the matter goes, there is no disadvantage of turning on TLS to the preferred mode. The only thing you may notice is the additional CPU overhead (to create the encrypted connection) but I would only expect this to be noticeable if your IronPort goes through a high rate of mail per second – you can always check the system status graphs before and after the changes to see if you notice anything abnormal.
This post goes through the changes in more detail regarding TLS on the IronPort so I would recommend you read the post @ https://supportforums.cisco.com/discussion/12191921/configuring-tls-ironport-esa
[…] you haven’t already, have a look at part 1 and part 2 of this […]